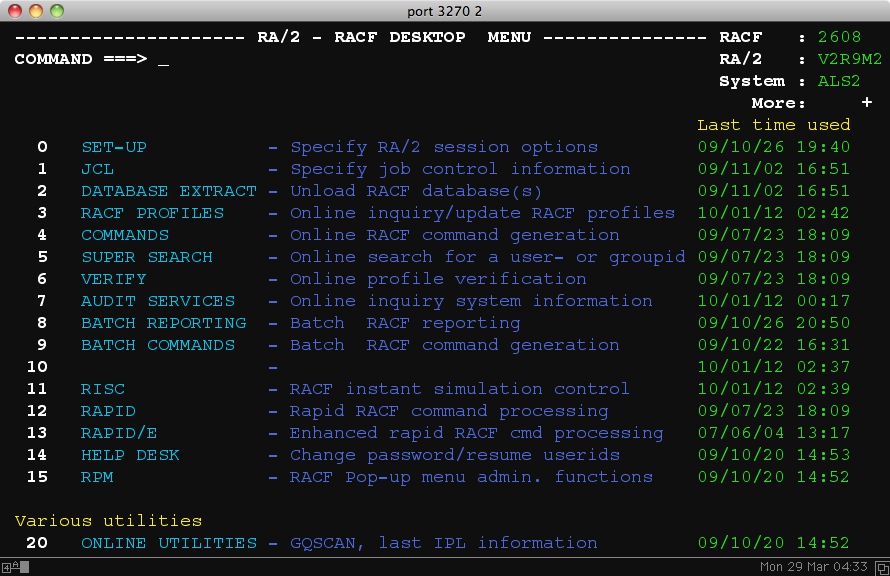
RA/2
RA/2 is designed to enhance IBM's RACF security system. A data center can expand their proficiency by utilizing RA/2 to make complex and comprehensive inquiries, from one easy to use product. RA/2 is a vital component in a RACF environment. RA/2 operates in both online and batch modes to perform comprehensive cross referencing for reporting, auditing and administrative tasks. RA/2 can also be used for making mass changes/additions to the RACF database, and RA/2 uses only standard RACF commands and facilities. RA2002 allows to administer the live RACF DB, whereby RA/2 utilizes an offloaded RACF DB.
Here are some of RA/2's highlights.
Features:
• Interfaces with IBM's IRRDBU00.
• Maintains data integrity by standardizing with IBM.
• Basic SMF Reporting. (User must consider RA/7 due to OMVS support)
• Analyze RACF SMF data online, or in batch, to identify all violations, warnings and errors for specified events.
• Decentralization.
• Scope of authority protection through decentralized RACF administration.
• Database recovery.
• Generates control cards to recreate the RACF database.
• Super Search Facility.
• Search for ANY and EVERY resource a USER or GROUP has access to.
• True Access Definition.
• Locate the true access all users/groups have to a specified resource based on all defined access attributes.
• Modify Resource Access - RISC Facility.
• Instantly display and modify resource access from within RA/2 or from any TSO command line or from ISPF data set display (ISPF 3.4) without knowing the profile protecting the resource and without having to process extensive RLIST or LISTDSD for relevant information.
• Analyze RACF Group Tree Structure.
• Display all group profiles in a TREE format showing the level of each group in relation to all other group profiles.
• Print/Search Facility allows users to print results of standard or customized profile reports.
• Define and modify user attributes online.
• Profile information at-a-glance through the display facility.